
Over the years, Threat actors have been deploying malware in emails via malicious Microsoft Word and Excel attachments, which then launch macros to download & install the malware.
Now attackers have targeted another Microsoft App, Mircosoft OneNote, in the same way, i.e., attaching malicious OneNote files in phishing emails to install remote access malware onto the victim’s computer to steal info regarding crypto wallet, passwords, or even installing other malware.
Don’t want to miss the best from TechLatest?
Set us as a preferred source in Google Search
and make sure you never miss our latest.
As we already know, OneNote is a note-taking app from Microsoft and is included with Microsoft Office & 365. With that being said, last year in July, Microsoft, by default disabled the macros again in Office Exel & Word, which ultimately made this technique useless.
Although that did not stop attackers as they started taking advantage of the new file formats such as ISO images & Zip files which are password protected! and on top of it, Windows Bug did help, too, by bypassing the security warnings & zip file archive utility not communicating the mark of the web to the extracted files.
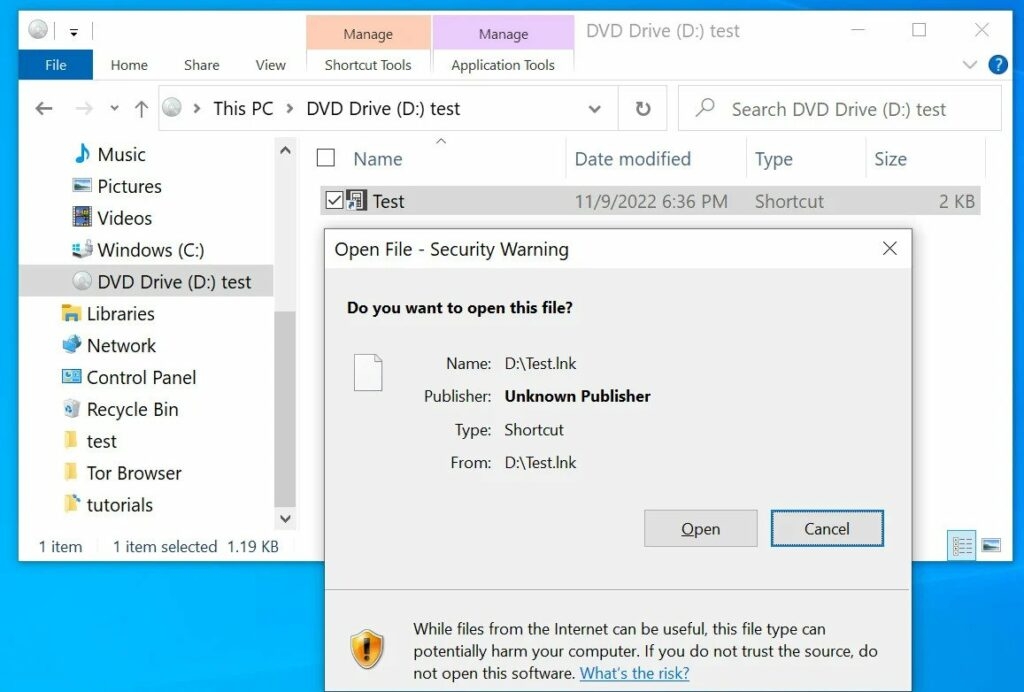
Well, these bugs were also fixed by Microsoft & 7 Zip which triggered frightening security messages when the user tried to open a download file in ISO & Zip files.
This did not stop threat attackers either, as they then switched to using a new file format using malicious spam attachments in Microsoft’s OneNote.
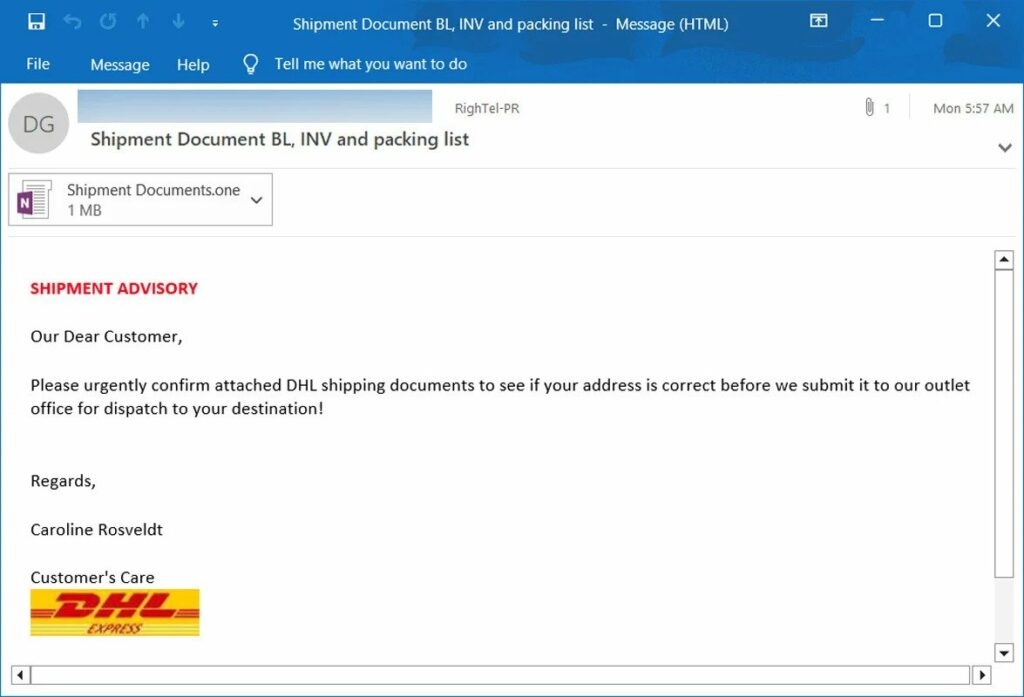
Various researchers from cybersecurity firms have already warned that the attackers have been distributing spam emails containing malicious OneNote attachments since Mid-December.
As per the samples found by the Bleeping computer, these spammy emails impersonated DHL shipping, invoices, shipping documents, mechanical drawings, and ACH remittance forms.
Microsoft OneNote does not support macros like Word or Excel, but it does allow the users to insert attachments into the notebook, and when it is double-clicked, it opens the attachment!
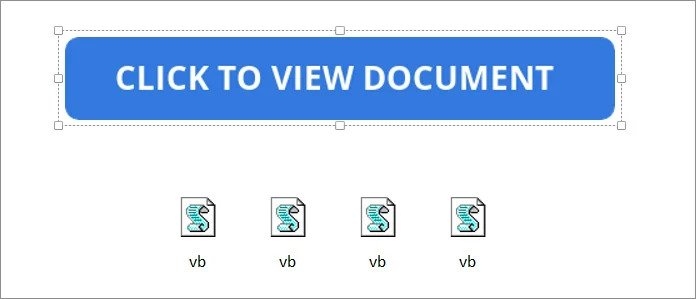
Threat attackers are taking advantage of this feature by using a VBS attachment that will automatically open the script when the users double-click it to download the malicious malware from a remote site and then install it.
The OneNote attachment simply looks like a file icon, so the attachers then put a big overlay that read double click to view files over the attached VBS files to hide them.
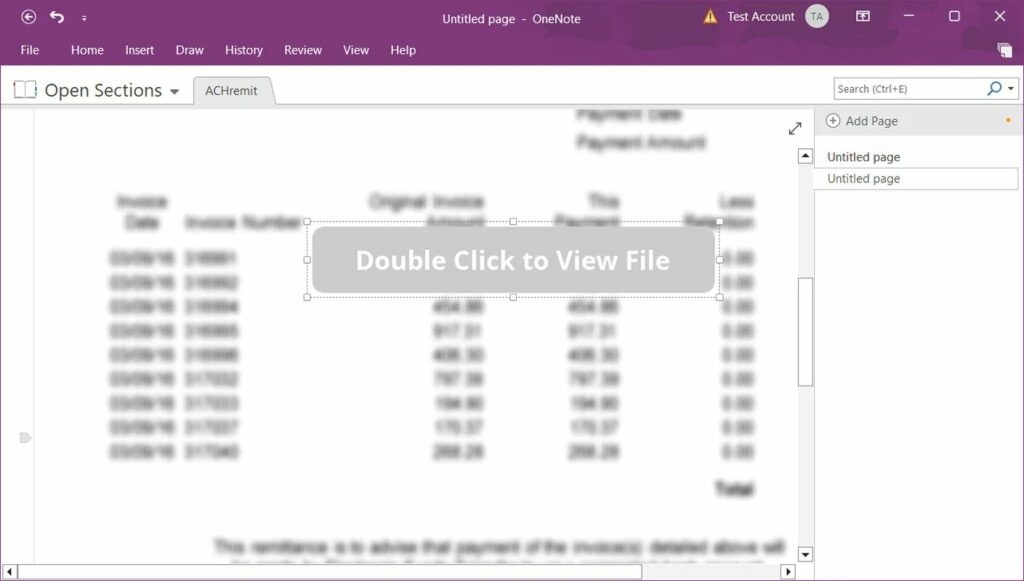
After that, when the user tries to move away from the Click to View Document bar, the malicious attachment has two attachments in it, and as there’s a line of attachments so if the user doubles click anywhere on the button, it will double click on the attachments to download it.
Just like any other file warning which comes you download from the internet! OneNote also warns the user before launching it but as we know, users tend to ignore it and click on OK instead.
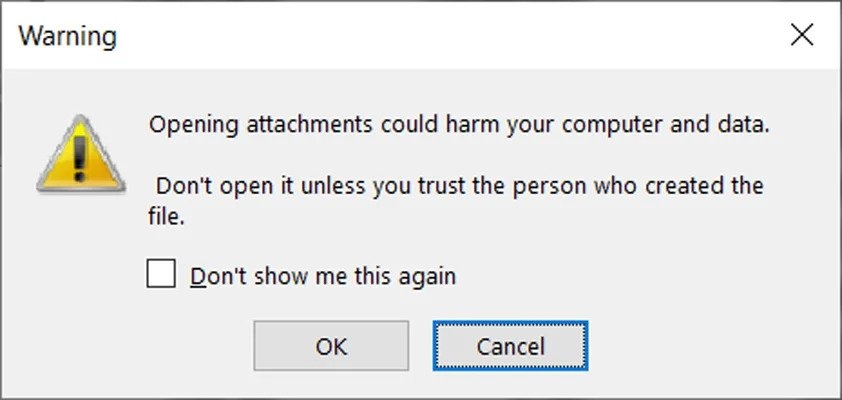
As soon as the user clicks on the OK button, it triggers the VBS script to download and then install malicious malware, and then the malicious VBS file downloads and runs two files from the remote server itself.
One example of such a luring OneNote document is that it appears to be a normal document, but in the background, the VBS file installs the malicious malware.
A cybersecurity researcher mentions that the OneNote attachments are installing Async and Xworm remote access malware. Another malware distributed by the threat actors is the Quasar remote access.
These kinds of trojan, once installed, lets the attackers remotely access the compromised device to steal files, browser password, etc., so it’s better not to install any unknown files as it could cause some major trouble.
Read: Cybercriminals Selling ‘Hook’ Android Malware for Remote Control of Smartphones
Enjoyed this article?
If TechLatest has helped you, consider supporting us with a one-time tip on Ko-fi. Every contribution keeps our work free and independent.
Support on Ko-fiDirectly in Your Inbox










