Highlights
- WordPress security firm, Defiant observed attacks exploit a flaw.
- The attack exploits an XSS flaw in a WordPress plugin named Beautiful Cookie Consent Banner.
- Attackers to make rouge Admin accounts on websites that can unpatched versions.

The WordPress security company, Defiant observed the attacks that target an Unauthorised Stored Cross-Site Scripting (XSS) exploit in a WordPress plugin named Beautiful Cookie Consent Banner, which has more than 40,000 active installs.
For starters, Cross Site Scripting is a type of injection in which the attacker injects malicious scripts into trusted websites. In XSS attacks, the threat actor sends a malicious code, as in the browser-side script, to a different user.
Don’t want to miss the best from TechLatest?
Set us as a preferred source in Google Search
and make sure you never miss our latest.
Well, the effect can include unauthorized access to sensitive information, session seizer, and malware infections via redirects to malicious or the full compromise of the victim’s system.
According to the WordPress security company, Defiant says that the exploit at issue also allows unauthorized attackers to make rogue admin accounts on websites that run unpatched plugin versions (up to & including 2.10.1). The vulnerability explained in this activity was patched in January with a newer version release, i.e., 2.10.2.
Read: CISA Warns of Samsung Devices’ Security Flaw, Allowing Android ASLR Bypass
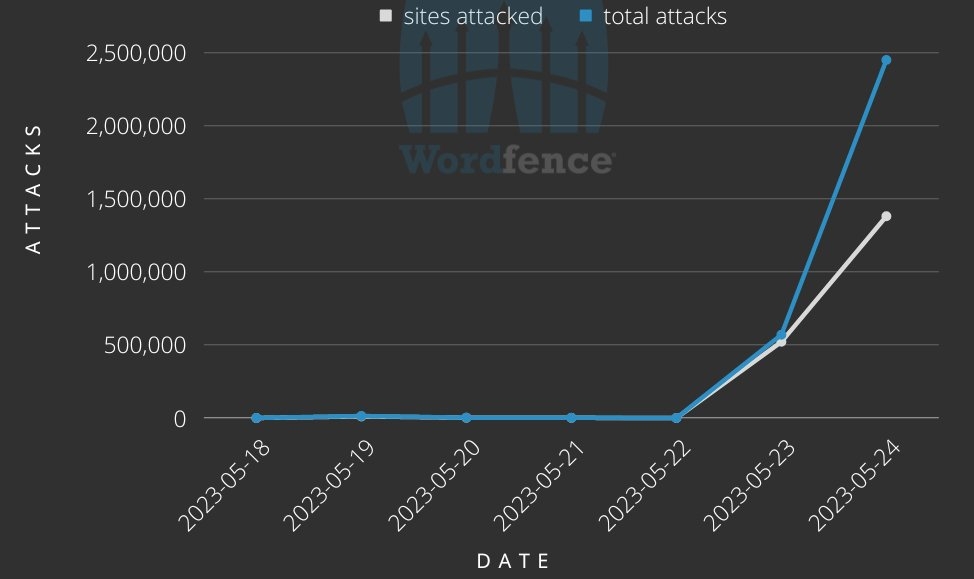
As per the threat analyst Ram Gall, the vulnerability has been actively attacked Since February 5, 2023, but this is the largest attack against it that we have seen. “We have blocked nearly 3 million attacks against more than 1.5 million websites from nearly 14,000 IP addresses since May 23, and attacks are ongoing.“
In spite of the large-scale nature of this attack activity, as per Gall, the threat actor uses a misconfigured exploit that would likely not deploy a payload even when targeting a WordPress site running a vulnerable plugin version.
Nonetheless, the admins or the owners of the website using a Beautiful Cookie Consent Banner plugin are advised to update the plugin to the latest version since a failed attack could corrupt the plugin configuration stored in the nsc_bar_bannersettings_json option.
Also, the patched plugin versions have also been updated to repair themselves in the event that the websites were targeted.
Although the recent wave of attacks might not be able to Inject with a malicious payload, the threat actors who are behind this activity could rectify these issues and likely infect those that remain exposed.
Read: Threat Actor Exploits Microsoft Azure to Gain Access to Virtual Machines
Enjoyed this article?
If TechLatest has helped you, consider supporting us with a one-time tip on Ko-fi. Every contribution keeps our work free and independent.
Support on Ko-fiDirectly in Your Inbox










