Highlights
- Cyber security firm traced a financially motivated cyber attacker.
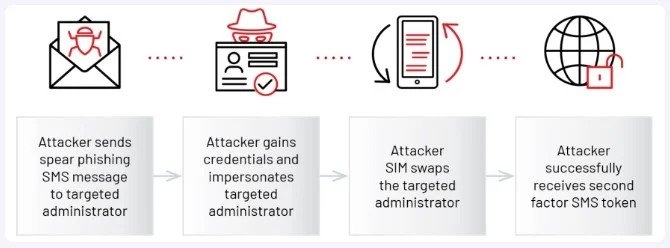
- The threat actor uses phishing attacks & SIM swapping.
- Threat actor takes control of the Microsoft Azure accounts to access the VMs.

Cyber security firm Mandiant traced a financially motivated cyber attacker named UNC3944 who is using phishing & SIM swapping to take control of Microsoft Azure admin accounts to gain access to the virtual machines.
According to cybersecurity firm Mandian report, UNC3944 has been active since May 2022, and their activity aims at stealing data from the infected organization using Microsoft cloud computing.
Don’t want to miss the best from TechLatest?
Set us as a preferred source in Google Search
and make sure you never miss our latest.
Also, The attacker UNC3944 has been previously attributed to creating the STONESTOP (Loader) and POORTRY (kernel mode driver) toolkit to stop security software.
The attackers utilize the Azure Serial Console to install remote management software for persistence and abuse Azure Extension for secretive surveillance. The attacker’s abused stolen Microsoft hardware developer accounts to sign their kernel drivers.
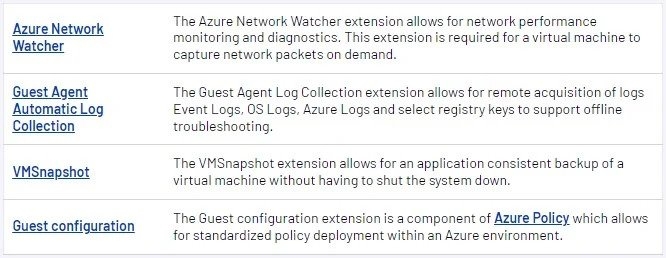
For those who don’t know, Microsoft Azure Extensions is an add-on feature & service that provides post-development configuration and automation tasks on Azure’s virtual machines.
Now, the initial access to the Microsoft Azure accounts takes place using the stolen credentials gained in SMS phishing, a usual UNC3944. After that, the threat attackers impersonate the manager when getting in touch with the help desk to trick them into sending a multi-factor reset code via SMS to the victim’s phone number.
Although the threat actor has already swapped SIM and ported it to their device, the attacker received the 2FA token without the target realizing it.
Read: Cactus Ransomware Exploiting VPN Weakness to Target Big Enterprises
However, the cybersecurity firm is yet to discover how the threat actors do the SIM swapping phase of their activity. Previous cases have pointed out that knowing the victim’s phone number and plotting with unethical telecom employees is sufficient to facilitate illicit number port.
As the attackers set up their footprint in the target organization’s Azure environment, the attacker uses the organization’s administrative privileges to collect information, modify their Azure accounts if needed or create new Azures accounts.
In this phase, the attacker utilizes Azure Extensions to run surveillance and gather information, disgusting their malicious activity as daily tasks and mixing up with the daily routine. Since these extensions are utilized inside the virtual machines and are usually used for authentic purposes, they are both secretive & less suspicious.
The attacker UNC3944 abuses the in-built Azure diagnostic extensions such as “CollectedGuestsLogs,” which was utilized for gathering log files from the breached endpoint. In addition to this, Mandiant has found proof of the threat actor trying to utilize these additional extensions.
Up next, UNC3944 uses Azure Serial Console to get administrative console access to virtual machines and run commands on a command prompt over a serial port.
In a report, the security firm mentions that the method of attacks was unique in that it avoided many of the conventional detection methods that are built in Azure and provided the attacker with administrative access to the VMs.
Furthermore, the cybersecurity firm observed that “whoami” is the first command the invader performs to identify the currently logged user & collect enough information to further the exploitation.
The attackers use Powershell to increase their persistence on virtual machines and then install a couple of commercially available remote administrator tools.
To maintain a presence on the VMs, the attacker frequently deploys a couple of commercially available remote administrator tools via PowerShell, reads the cybersecurity firm report.
Well, the advantage of these tools is that they are authentic signed applications and give the attacker remote access without notifying many endpoints in the detection platforms.
In the next phase, UNC3944 creates a reverse SSH tunnel to the C2 server to keep stealthy & persistent access via a safe channel and avoid any network restrictions & security controls.
UNC3944 configures the reverse tunnel with port forwarding, making a direct connection to the Azure virtual machine via the Remote Desktop.
For instance, any incoming connection to a remote machine port 12345 would be forwarded to the local host port 3389, that is (RemoteDesktop Protocol Service Port).
At last, the attackers utilize the credentials of an infected user account to log in to the compromised Azure VM via the reverse shell. They only then proceed to expand their control within the breached environment, stealing critical information along the way.
The attacks tracked by the security firm show that UNC3944 has a deep understanding of the Azure environment and how they can take advantage of built-in tools to avoid detection & social engineering skills to perform SIM swapping, which makes the risk much bigger than it already is.
Read: ChatGPT Now Browses the Internet for Better Accuracy in Responses
Enjoyed this article?
If TechLatest has helped you, consider supporting us with a one-time tip on Ko-fi. Every contribution keeps our work free and independent.
Support on Ko-fiDirectly in Your Inbox










