
CircleCi, a popular CI/CD (Continuous Integration & Continuous Development) platform used for DevOps practices revealed that it suffered a security exploit.
In December last year, an engineer at CircleCi became infected with information-stealing malware, which the hackers used to breach their 2FA-backed SSO session cookie, which allowed the attackers access to CircleCi’s internal systems.
Don’t want to miss the best from TechLatest?
Set us as a preferred source in Google Search
and make sure you never miss our latest.
A report published by CircleCi, the CI/CD platform mentions that they learned about the security exploit after a customer reported that their GitHub OAuth code has been compromised. This incident led to the company spinning its customer’s GitHub Auth codes automatically!
The information-stealing malware stole the corporate session cookie, which had been already authenticated via the 2FA, which allowed the attackers to login in as users without having to authenticate it.
Furthermore, the malware was able to execute session cookie theft which thereby enabled the hackers to impersonate the employee they were targeting in a remote location and then amplify access to the sub-net of the production systems.
So the attackers started stealing data from the company database & stores, which includes keys, tokens, and customer environment variables, using the engineer’s authorization.
Although CircleCi had encrypted the data, the attackers stole the encrypted keys as well by throwing them into the running process, which possibly allowed the attackers to de-encrypted the encrypted data that was stolen.
As soon as the company learned about the security breach, they sent an email to customers notifying them to spin all their tokens & secrets if they logged in after 21 December.
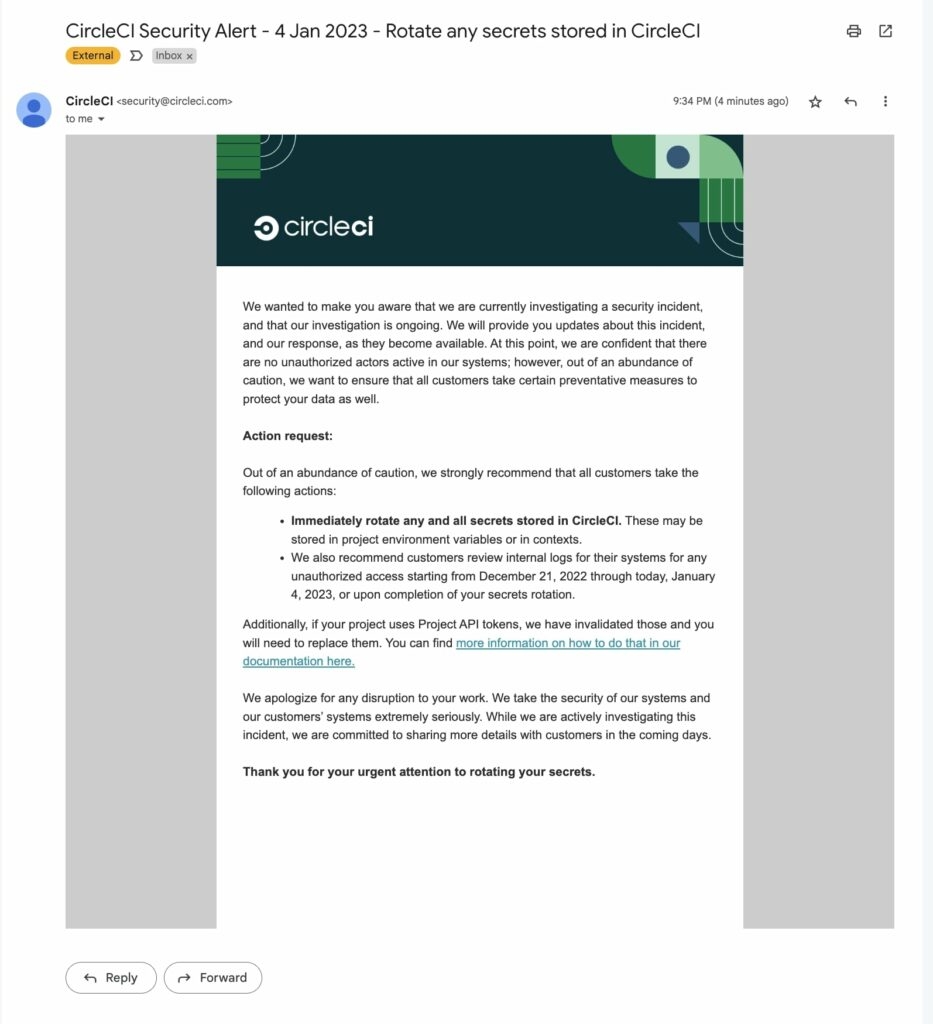
The company mentions that they have already spun all the tokens belonging to their customers, which include GitHub OAuth, Personal API tokens, and Project API tokens. In addition to this, CircleCi also worked with AWS and Atlassian to inform the customers of likely compromised Bitbucket tokens & AWS tokens.
To prevent incidents like these from happening, the company strengthened its infrastructure by adding further detection for the behavior displayed by the information-stealing malware to the antivirus and the Mobile Device Management they use.
Moreover, the company has now further narrowed access to its production environment to a smaller number of people and simultaneously increased the security of the 2FA implementation.
Now all these attacks on the companies are simply instances of the increased targeting done by attackers on the Multi-factor authentication implemented by the companies, whether by doing Phishing attacks or information-stealing malware.
As we know, MFAs are implemented by companies to prevent any unauthorized access to their system. However, with the increased usage of the MFAs, the attackers have also evolved and are using tactics like stealing session cookies which are already authenticated by the MFA Fatigue on the MFA implemented by these companies.
It is very important for companies to configure these platforms correctly so that they can detect when the session cookie is being used from a remote location and then request further MFA access.
Read: 6 Malicious PyPi Packages Installing RAT Malware via Cloudflare Tunneling
Enjoyed this article?
If TechLatest has helped you, consider supporting us with a one-time tip on Ko-fi. Every contribution keeps our work free and independent.
Support on Ko-fiDirectly in Your Inbox










