Highlights
- Equinix Threat Analysis Centre discovered a new variant of the Royal Trojan.
- Royal Ransomware is privately owned by a number of experienced threat actors.
- It is using Linux to target VMware ESXi virtual systems.

A security researcher named Will Thomas at Equinix Threat Analysis Centre (ETAC) discovered a new variant of the Royal Trojan which is performed using a command line.
Thus the Royal trojan becomes the latest trojan that has added support for encrypting Linux devices to its variants, especially targeting VMware ESXi virtual systems.
Don’t want to miss the best from TechLatest?
Set us as a preferred source in Google Search
and make sure you never miss our latest.
There have been several incidents of similar Ransomware encryptors pushed out by the groups AvosLocker, Hive, Black Basta & more.
Also, it supports multiple flags, which gives the ransomware operators some control over the encryption process. These are the following flags.
-stopvm > stop all running VMs so they can be encrypted.
-vmony - Only encrypt virtual machines
-id: id must be 32 characters.
-fork - unknown
-logs - unknown Now when the ransomware encrypts the file, it adds the .royal_u extension to all the encrypted files on the VM.
Although the Anti-ransomware mechanisms have had issues detecting the ransomware but have now detected 23 of the 63 malware scanning engine on Virus Total.

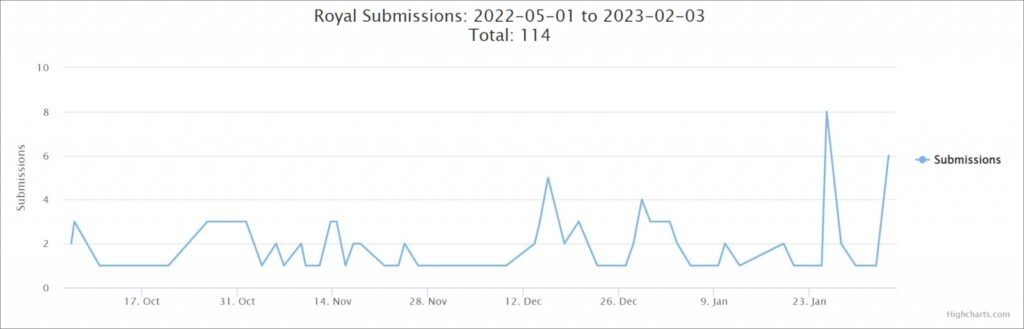
For those who do not know, Royal Ransomware is privately owned by a number of experienced threat actors who had previously operated Conti ransomware. Royal ransomware was first found in January 2022, and in September, Royal increased its malicious activities.
At first, the threat actors used encryptors from other operations like BlackCat and then changed to using their own, like Zoen, which sent ransom notes just like those sent by Conti ransomware.
Read: Attackers Abusing OneNote Attachments to Spread RAT Malware
In September, the threat attackers rebranded the strain as Royal and then started deploying a new encryptor in attacks that sent ransom notes with the exact same names.
After that, the group demands a ransom after encrypting their target’s enterprise network systems.
The US Department of Health and Human Services also warned against royal ransomware targeting the Healthcare and public sectors.
This isn’t the first time the threat attackers are targeting ESXI virtual machines simply since the companies started using the VMs as they improved their device management and much more efficient resource handling.
As they deploy payload on ESXi hosts, the threat attackers use a single command to encrypt multiple servers. One thing to note here is that the groups implemented ransomware based on Linux that targets ESXi.
Many VMware ESXi servers all over the internet got their last bit. They will only get technical support now but will only get security updates, making them susceptible to ransom attacks.
Read: Netflix’s Strict Measures on Password Sharing: What to Expect
Enjoyed this article?
If TechLatest has helped you, consider supporting us with a one-time tip on Ko-fi. Every contribution keeps our work free and independent.
Support on Ko-fiDirectly in Your Inbox










