Highlights
- Royal Ransomware is a ransomware group consisting of ones associated with Conti.
- Security researchers discovered attacks that used their own branded encryptor named Blacksuit.
- It is believed that these were the activity when ransomware would re-brand itself, but there was no rebrand.

Royal Ransomware is a ransomware group consisting of the pen-testers and the ones associated with Conti Team 1, and the other recruits from the other ransomware gangs that target organizations. Launched in 2023, and is believed to be the successor of Conti, which shut down in June 2022.
Since its inception, Royal Ransomware has been very active and is responsible for several attacks on enterprises, and it seems that Royal Ransomware Group has started testing a new encryptor named Blacksuit that has many similarities with the regular campaign encryptor.
Don’t want to miss the best from TechLatest?
Set us as a preferred source in Google Search
and make sure you never miss our latest.
There has been enough rumble from last April that the Royal ransomware was getting re-branded under a new name. This became more serious as the ransomware group felt pressured by law enforcement after they attacked the city of Dallas, Texas.
In May, cybersecurity researchers discovered attacks that used its own branded encryptor & Tor negotiation, and it is believed that these were the campaigns that the Royal ransomware would rebrand into, but as it turns out, there was no re-brand, the ransomware group is still attacking the organizations and is using Blacksuit in fewer attacks.
Yelisey Bohuslavskiy, Partner & Head of R&D in RedSense, posted on LinkedIn that Royal, the direct heir of Conti, consisting of over 60 pen testers, either from Conti’s old Gaurd or recruited from various elite ransomware groups. Operating in small groups of 4-5 individuals, they remain loyal to their leaders.
Read: New Royal Trojan Variant Discovered, Targets VMware ESXi Virtual Machines
The ransomware group employs Blacksuit & Royal Loader, with Emotet and IcedID as forerunners. They prioritize alternatives to CobaltStrike, especially Silver, and develop custom forerunners.
According to Bohuslavskiy, it is viable that the ransomware group is simply testing a new encryptor as they have been with other tools used by them, including a new loader IcedID and reinvigorating Emotet
They also keep improving the Emoled to reinvigorate it and are also working on IcedID a lot. Their experiments with new lockers are natural in that sense, mentions Bohuslavskiy.
In addition to this, Bohuslavskiy said we might see more things like Blacksuit soon. But so far, it seems that both the new loader and Blacksuit locker were a failed experiment.
Since Blacksuit is self-contained activity, Royal is likely planning on starting a subgroup focused on specific types of victims, or it is being kept for a rebrand later down the line. Although, we may not see a rebrand as there are clear similarities between Blacksuit and Royal Ransomware, highlighted in a report by Trend Micro.
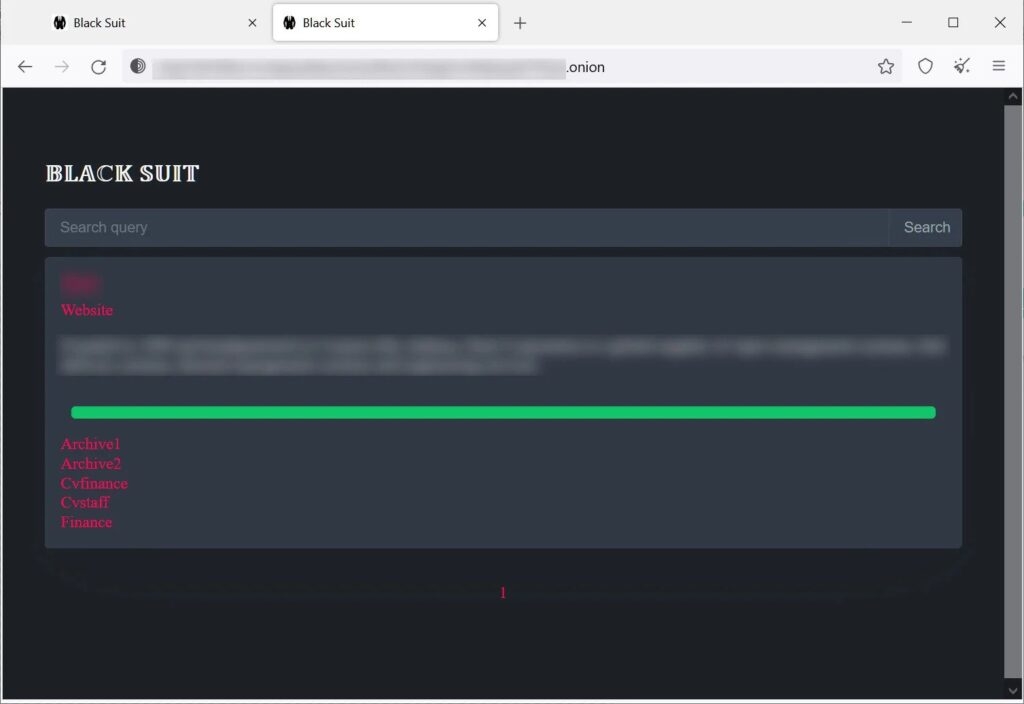
The similarities include code similarities, file inclusion & more. Although, it is unclear how blacksuit will be used. It is still being used in some of the attacks. As of now, there is only one victim listed on their data leak website though it can change very fast if the new encryptor is more heavily used.
Read: The Dark Pink Hackers Group Targeting Military & Government Organizations
Enjoyed this article?
If TechLatest has helped you, consider supporting us with a one-time tip on Ko-fi. Every contribution keeps our work free and independent.
Support on Ko-fiDirectly in Your Inbox










