A new malware that steals information named RisePro has been found and is being spread through the fake cracked websites operated by the PrivateLoader (Pay Per Install), a malware distribution service.
The experts at Flashpoint & Sekoia discovered the RisePro malware and have thus confirmed that this RisePro malware is a previously unrecorded information stealer that is now being spread via fake software cracks and key generators.
Don’t want to miss the best from TechLatest?
Set us as a preferred source in Google Search
and make sure you never miss our latest.
The RisePro malware has been created to help the threat actors steal the victim’s passwords, credit card information, and cryptocurrency wallets.
Flashpoint mentioned that the threat attackers have already started selling thousands of the logs of RisePro logs (Data stolen from the compromised devices) on the Russian dark web markets.
In addition to this, the analysts at the Sekoia found substantial code similarities between the PrivateLoader, which suggests that the malware-distribution platform is spreading its own information stealer for itself or is either selling it as a service.
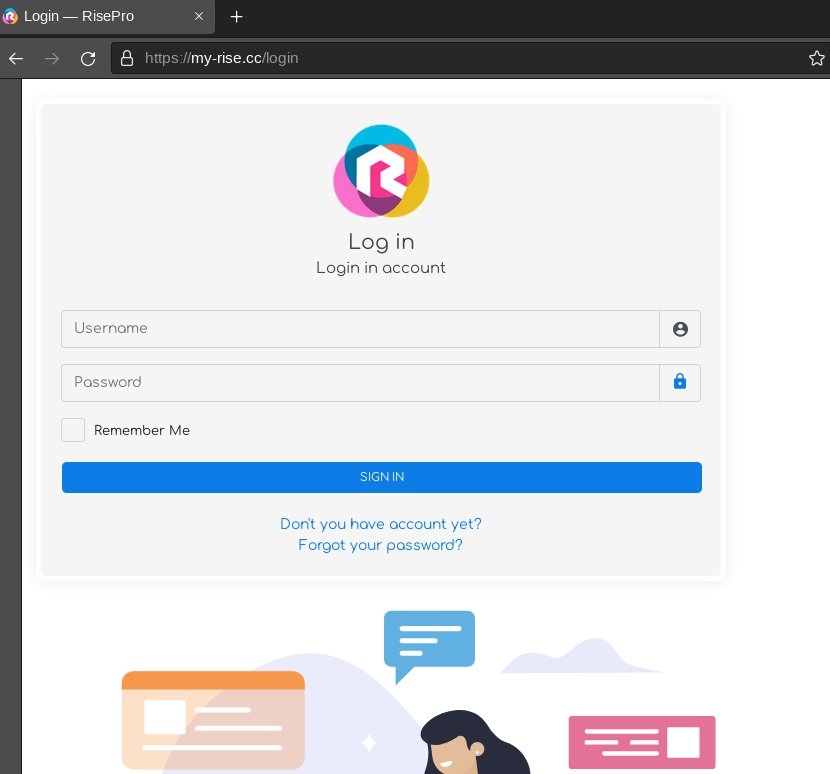
As of now, the information-stealing malware is being sold on Telegram, where the users interact with the developer and the compromised telegram BOT.
RisePro is a C++ malware that, as per Flashpoint, might be built on Vidar password-stealing malware as it uses the same system of enabled DLL dependencies.
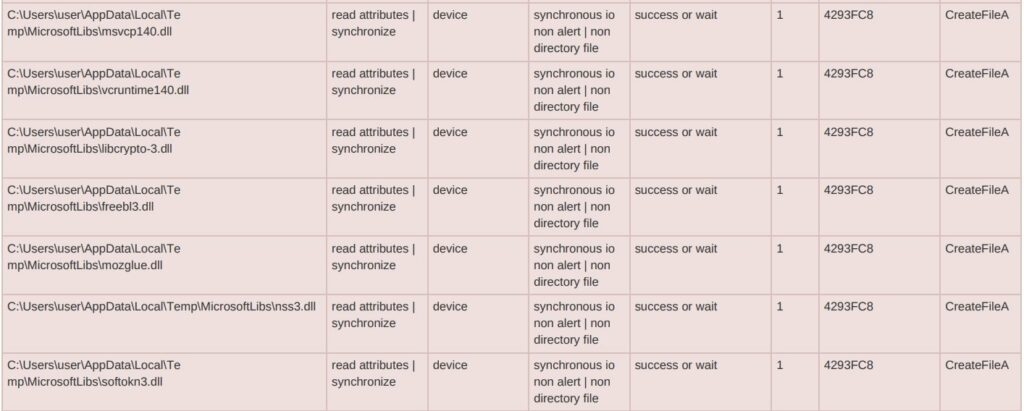
Furthermore, Sekoia says that some samples of the RisePro enabled the DLLs, whereas, in others, the malware collected them from the C2 server using the POST requests.
Well, the malware first separates the infected system by inspecting the registry keys, writes the stolen data to the test file, takes the screenshot, bundles it in a ZIP file, and then sends the ZIP file to the threat attacker’s server.
RisePro malware tries to steal different kinds of data from applications, crypto wallets, and browser extensions, as listed below.
Software– Discord, battle.net, Authy Desktop.
Cryptocurrency wallets – Bitcoin, dogecoin, DashCore, Franko, infinitecoin, Ixcoin, Megacoin, Minicoin, Namecoin, Primecoin, Terracoin, YAcoin, Zcash, Reddcoin, digitalcoin, devcoin.
Web browsers – Google Chrome, Firefox, MetaMask, Torch, Comodo, Chromium Elements, 7start, Netbox, CentBrowser, Orbitum, Amigo, Opera, Brave, Vivaldi, and more.
Browser Extensions – Jxx liberty extension, MetaMusk, iWallet, SaturnWallet, GuildWallet, MewCx, Wombat, NiftyWallet, Neoline, RoninWallet, BainanceChainWallet, Yoroi, EQUALWallet, BoltX, and more.
Moreover, the information stealer malware can also scan file system folders for compelling data like receipts containing credit card information.
Read: Godfather Android Malware Stealing Bank Websites & Crypto Exchanges’ Data
As mentioned, the malware was being spread by the PrivateLoader, (A Pay Per Install) which disguised itself as a service for cracked software, key generator, and game modifications.
The threat actors give the malware sample they hope to spread, targeting basis, and payment to the PrivateLoader team, which uses their website to fake and hack websites to spread malware.
The PrivateLoader malware distributing service was first seen by Intel471 in February 2022 and then TrendMicro spotted PrivateLoader pushing a New Remote Trojan, named NetDooka.
Also, the information distribution service is almost exclusively either Rocoin, Redline, (famous information steeler).
Sekoia, the security firm, said that it found loader capabilities in the new malware, highlighting that this part extensively overlays with the PrivateLoader.
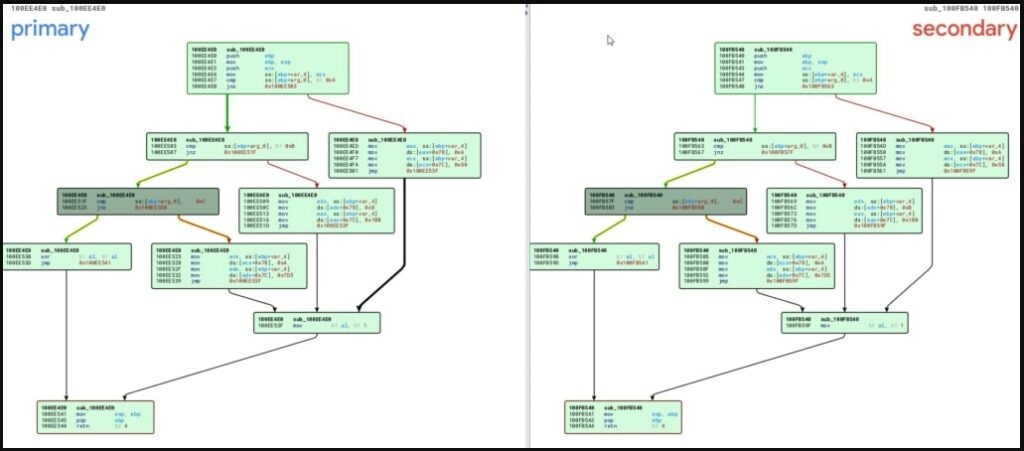
The similarities were the HTTP & port setup and the strings obfuscation method.
It is possible that the malware-spreading service developed the RisePro or the evolution of the PrivateLoader.
Read: Attackers Exploit a Flaw in YTTH WooCommerce Gift Card Premium Plugin
Enjoyed this article?
If TechLatest has helped you, consider supporting us with a one-time tip on Ko-fi. Every contribution keeps our work free and independent.
Support on Ko-fiDirectly in Your Inbox










