Highlights
- OpenAI’s ChatGPT is an Ai-powered chatbox built on GPT family 3 of the large language model.
- Threat actors use ChatGPT’s popularity to distribute malware for Windows and Android.
- Attackers promoted phishing websites through a Facebook page & used fake ChatGPT apps to install malware & steal info.

As you may have been already familiar with the Open Ai’s ChatGPT. Well, ChatGPT is a chatbox, built on GPT family 3 of the large language model.
It rose to fame in November last year and soon gained more than 100 million users all over the globe. It is an AI-powered Chatbox which can be used for writing essays, coding software, recipes, etc.
Don’t want to miss the best from TechLatest?
Set us as a preferred source in Google Search
and make sure you never miss our latest.
Now, Threat actors are using ChatGPT popularity to distribute malware for Windows and Android or are simply directing the unwary to the phishing page.
Due to immense popularity and growth enforced, the company behind ChatGPT, i.e., OpenAI, restrained the use of the tool, and the company then launched a $20 per month service named ChatGPTPlus for those who want to use the tool with no restrictions.
Read: 10 Coolest Things you can do with ChatGPT
This change gave threat actors the perfect opportunity to take advantage of the fame of the tool to promise unrestricted and no fees required to access the ChatGPTPlus. These are fake offers, and the only goal is to lure the users into installing the malware or stealing their account information.
Dominic Alvieri was among the security researchers who observed one such instance using the domain chat-gpt-pc-.online to infect the users with the Redline information-stealing malware under the appearance of a download for the ChatGPT Window Desktop client.
Well, the website was promoted via a Facebook Page that used the ChatGPT logos to fool users into getting redirected to the malicious website.
Furthermore, the security firm Cyble has published some additional information in relation to the malware distribution campaign spotted by Alvieri, as other malicious campaigns taking advantage of the ChatGPT fame. Cyble found that “chatgpt-go-online” spread malware that stole the Aurora stealer and the clipboard contents.
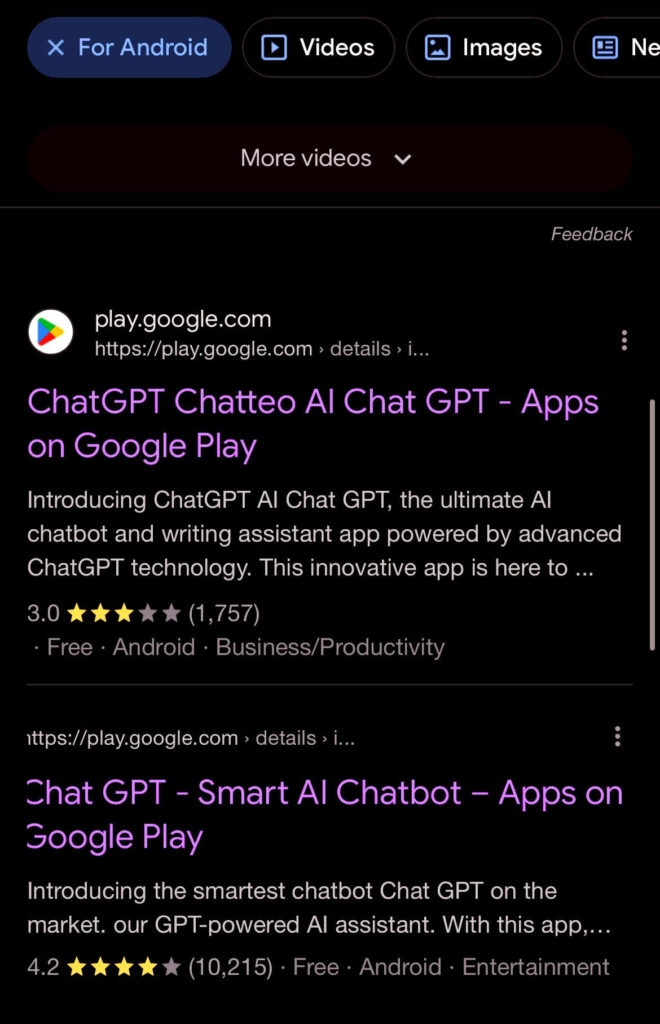
Also, Alvieri spotted fake ChatGPT apps being promoted on Google Play Store and third-party Android app stores to push suspicious software onto user’s devices.
In addition to this, chat-gpt-pc[.]online carried lumma stealer in security research firm tests, and another domain, “openai-pc-pro[.]online” delivers an unidentified malware family.
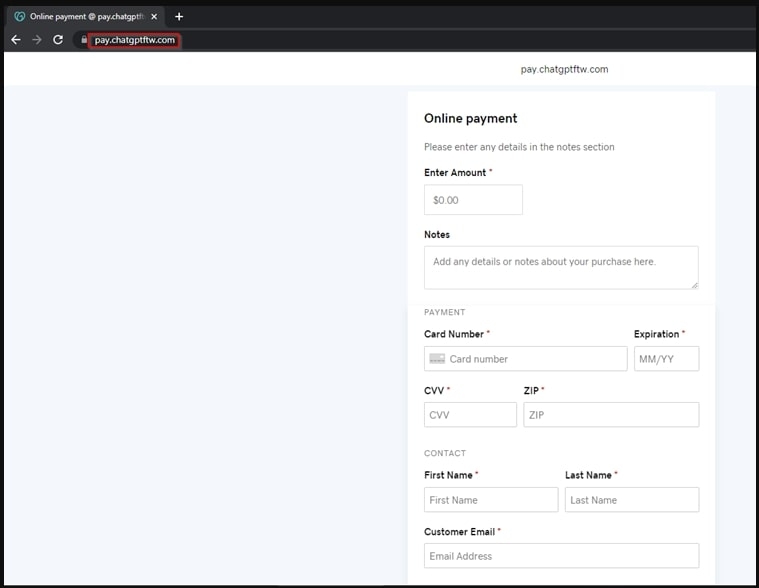
Cyble also discovered a credit card stealing page at “pay.chatgptftw.com” which apparently gives the visitors a payment portal to buy ChatGPT Plus.
As we mentioned above, fake apps were being used. Now, Cybil found more than 50 apps that use ChatGPT’s icon and identical names; almost all are fake and are trying to harm the user’s devices.
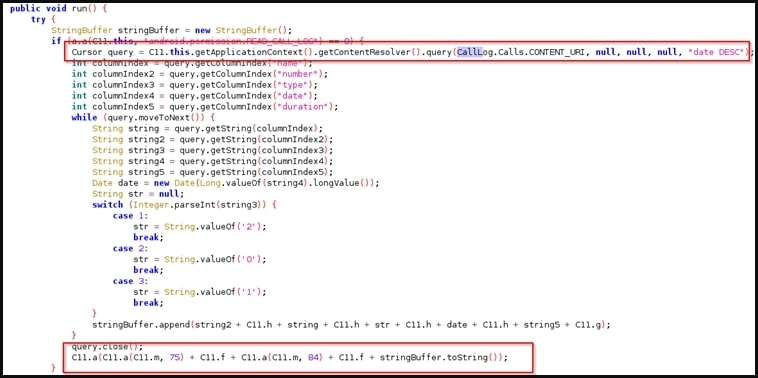
The security firm highlights two examples in its report that being the chatGPT1, which is an SMS billing fraud application and the AI photo, which consists of Spynote malware that can steal SMS, Contact lists, call logs and files from the devices.
ChatGPT is currently available only at chat.openai.com, so any apps or websites claiming to be ChatGPT is totally fake & malicious.
Read: ProxyShellMiner Malware Exploits Vulnerabilities for Cryptocurrency Mining
Enjoyed this article?
If TechLatest has helped you, consider supporting us with a one-time tip on Ko-fi. Every contribution keeps our work free and independent.
Support on Ko-fiDirectly in Your Inbox










