
Security researchers at Trend Micro are back with the discovery of a new ransomware which the researchers named Mimic, that takes advantage of APIs of the Everything file search tool for windows to search for files that are targeted for encryption.
‘Mimic’ was discovered in June of last year, and it seems like the ransomware targets users who speak Russian & English.
Don’t want to miss the best from TechLatest?
Set us as a preferred source in Google Search
and make sure you never miss our latest.
The security researchers at Trend Micro found similarities between some of the codes of Mimic and Condi ransomware, whose source code got leaked by a Ukrainian researcher back in March 2022.
As you may have guessed, Condi is also very dangerous ransomware because of how fast it encrypts data and spreads to other systems.
The ransomware is believed to be backed by Russian-based cyber criminals who use the pseudonym of Wizard Spider. The Russian group performs phishing attacks to install TrickBot & Bazarloader malware to get Remote access to the infected device.
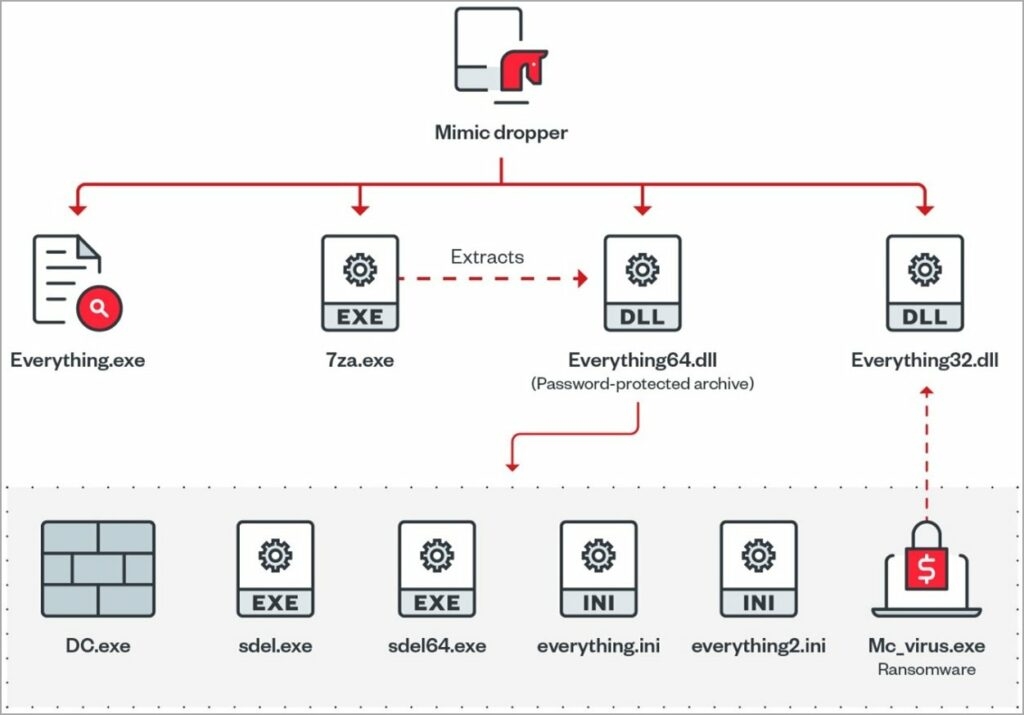
Now that you know Condi, let us see how Mimic works; Mimic ransomware starts its attack after the target receives an executable, supposedly through an e-mail which then extracts the four files onto the targets system, including ancillary files, the main payload, and the mechanisms to stop Windows Defender.
With that, Mimic is flexible ransomware that supports the command-line arguments to narrow file targeting. Also, it can use multiple processor threads to accelerate the data encryption process.
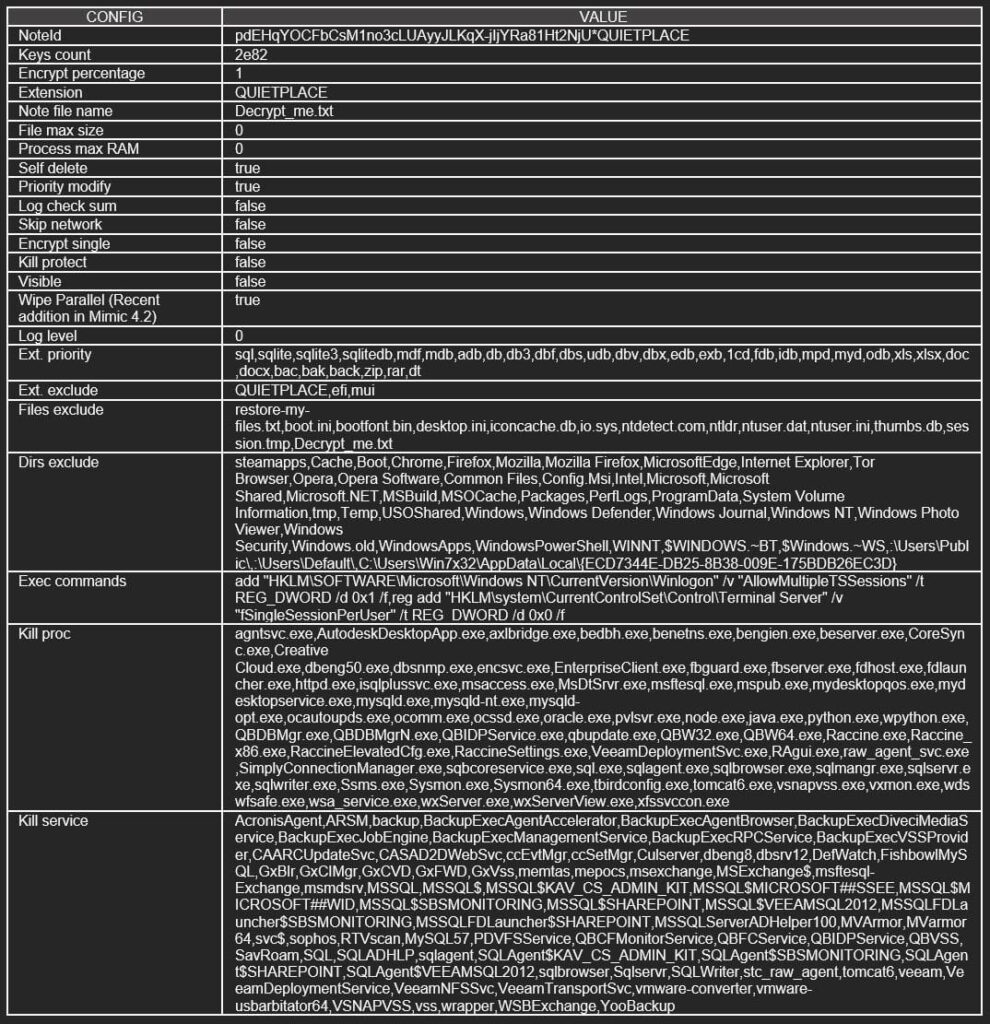
Researchers found several capabilities in Mimic that are found in present-day ransomware. These capabilities include
- Collecting the user information
- Bypassing User Account Control
- Activativating Anti Shutdown measures
- Activating Anti Kill measures
- Creating persistence through RunKey
- Unmounting Visual Drivers
- Disabling Windows telemetry
- Terminating processes and services
- Disabling sleep mode and Shutdown
- Removing Indicators
- Hamper System Recovery
By terminating the processes & services, it aims to disable the data protection procedure and then free up valuable data like the database files and, thus making them accessible for encryption.
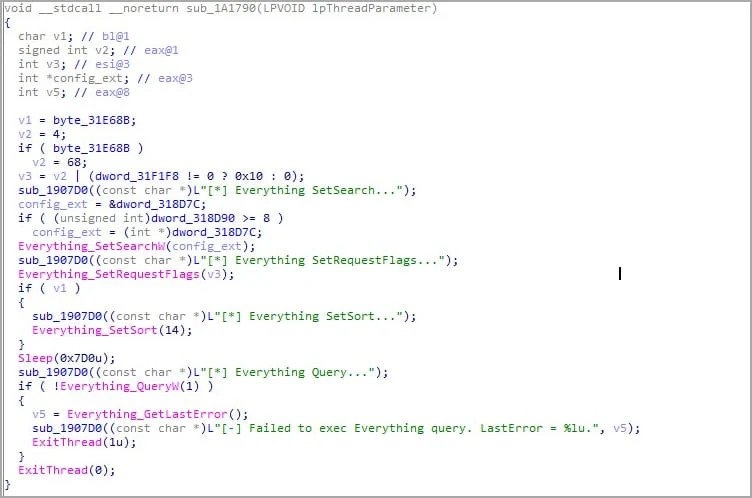
For those unaware, Everything is a filename search engine for windows, uses minimum resources, and is light. The new ransomware uses the Everything search in the form of Everything32.dlll, which it releases when it is in the infection phase to query for a particular name and extension on the infected system.
The file search engine helps the ransomware find the files which are valid for encryption and meanwhile dodging the system files which would render the system unbeatable if locked.
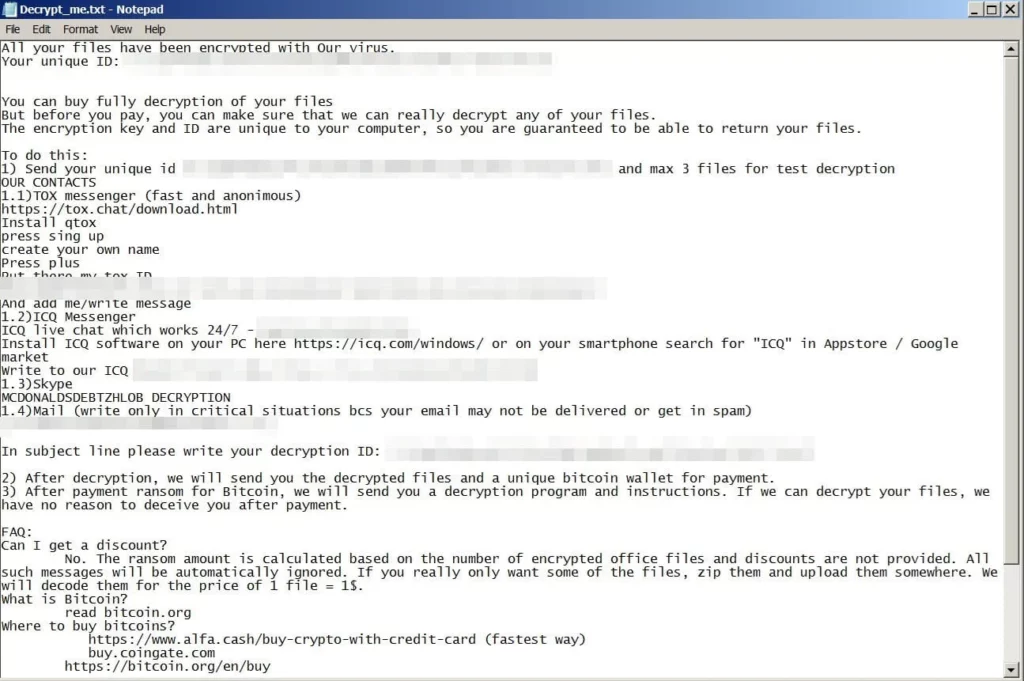
After that, the files that are encrypted by Mimic get the ‘QUITEPLACE’ extension, and with that, a Ransome message is flashed onto the compromised machine notifying the victim about it.
Currently, there are no activities relating to the ransomware, but the code similarities with the Conti Ransome, which proves that the attackers know what they’re doing.
Read: Attackers Abusing OneNote Attachments to Spread RAT Malware
Enjoyed this article?
If TechLatest has helped you, consider supporting us with a one-time tip on Ko-fi. Every contribution keeps our work free and independent.
Support on Ko-fiDirectly in Your Inbox










